Digital Activity Documentation Linked to 66.29.129.121 and Alerts Logs
Digital activity documentation associated with the IP address 66.29.129.121 is essential for understanding user interactions and system functionality. By closely examining the digital activity logs, analysts can identify anomalies that may indicate security vulnerabilities. Alert notifications serve as critical indicators of these irregularities, prompting further investigation. This process not only enhances user experience but also maintains network integrity. The implications of such practices warrant a deeper exploration of their effectiveness and potential improvements.
Overview of IP Address 66.29.129.121
The IP address 66.29.129.121 serves as a unique identifier within the Internet Protocol suite, enabling devices to communicate over networks.
Through IP geolocation, analysts can pinpoint the geographical origin of this address, revealing insights into traffic patterns.
Understanding these dynamics is crucial for enhancing network security and optimizing data flow, ultimately empowering users to navigate the digital landscape with greater autonomy and awareness.
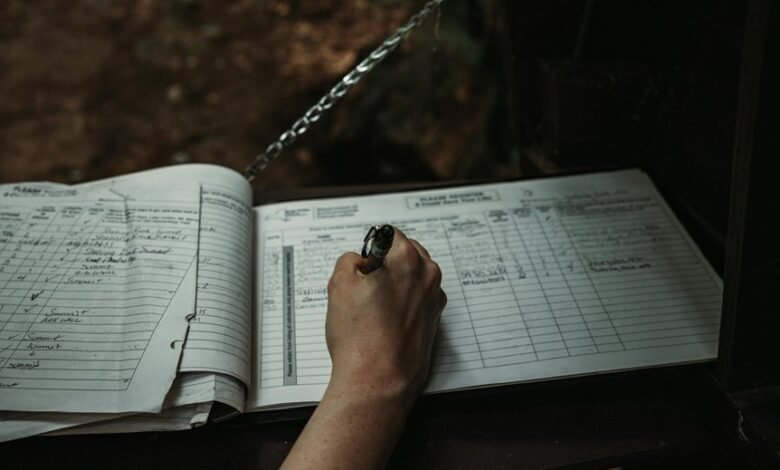
Analysis of Digital Activity Logs
How can the analysis of digital activity logs enhance understanding of user behavior and system performance?
By employing log correlation techniques, analysts can identify patterns and trends, facilitating anomaly detection. This process reveals deviations from expected behaviors, enabling proactive measures to optimize system functionality.
Consequently, a comprehensive examination of these logs empowers organizations to enhance user experiences and ensure robust system integrity.
Alert Notifications and Their Implications
Alert notifications serve as critical indicators within digital systems, providing real-time insights into user activities and system performance.
Effective notification systems enhance alert response capabilities, enabling swift identification of anomalies or breaches. This immediacy fosters a proactive approach to security, allowing users the autonomy to address potential threats.
Consequently, the implications of alert notifications extend beyond mere awareness, influencing strategic decision-making in digital environments.
Best Practices for Cybersecurity and Monitoring
Implementing best practices for cybersecurity and monitoring is essential for safeguarding digital infrastructures. Organizations should adopt robust cybersecurity frameworks that prioritize proactive threat detection.
Regular audits, employee training, and real-time monitoring systems enhance resilience against evolving threats. Furthermore, integrating automated response mechanisms ensures rapid mitigation of incidents, fostering an environment where digital freedom can thrive without compromising security.
Conclusion
In conclusion, the digital activity documentation associated with IP address 66.29.129.121 is integral to maintaining a secure network environment. While some may argue that constant monitoring infringes on user privacy, the proactive identification of anomalies and potential security threats ultimately enhances user experience and system integrity. By adhering to best practices in cybersecurity and vigilant monitoring, organizations can ensure that users benefit from both security and privacy, fostering a safer online space for all.





